
Introducing effective settings: See security configurations enforced on your device techcommunity.micros...
#MicrosoftDefender #DefenderforCloud #Security #MicrosoftSecurity #Cybersecurity #DefenderXDR #MicrosoftThreatIntelligence
Latest posts tagged with #DefenderForCloud on Bluesky

Introducing effective settings: See security configurations enforced on your device techcommunity.micros...
#MicrosoftDefender #DefenderforCloud #Security #MicrosoftSecurity #Cybersecurity #DefenderXDR #MicrosoftThreatIntelligence

Scaling security operations with Microsoft Defender autonomous defense and expert-led services www.microsoft.com/en...
#MicrosoftDefender #DefenderforCloud #Security #MicrosoftSecurity #Cybersecurity #DefenderXDR #MicrosoftThreatIntelligence

From signal to strategy: Closing attack paths with identity intelligence techcommunity.micros...
#MicrosoftDefender #DefenderforCloud #Security #MicrosoftSecurity #Cybersecurity #DefenderXDR #MicrosoftThreatIntelligence

New built‑in Alert Tuning rules in Defender socautomators.substa...
#MicrosoftDefender #DefenderforCloud #Security #MicrosoftSecurity #Cybersecurity #DefenderXDR #MicrosoftThreatIntelligence

New Clickfix variant ‘CrashFix’ deploying Python Remote Access Trojan www.microsoft.com/en...
#MicrosoftDefender #DefenderforCloud #Security #MicrosoftSecurity #Cybersecurity #DefenderXDR #MicrosoftThreatIntelligence

Extending Defender’s AI Threat Protection to Microsoft Foundry Agents techcommunity.micros...
#MicrosoftDefender #DefenderforCloud #Security #MicrosoftSecurity #Cybersecurity #DefenderXDR #MicrosoftThreatIntelligence

Architecting Trust: A NIST-Based Security Governance Framework for AI Agents techcommunity.micros...
#MicrosoftDefender #DefenderforCloud #Security #MicrosoftSecurity #Cybersecurity #DefenderXDR #MicrosoftThreatIntelligence

Splitting single-tenant Microsoft Defender XDR Sentinel logs in multiple company scenarios techcommunity.micros...
#MicrosoftDefender #DefenderforCloud #Security #MicrosoftSecurity #Cybersecurity #DefenderXDR #MicrosoftThreatIntelligence

Turning threat reports into detection insights with AI www.microsoft.com/en...
#MicrosoftDefender #DefenderforCloud #Security #MicrosoftSecurity #Cybersecurity #DefenderXDR #MicrosoftThreatIntelligence

Threat Analytics in Microsoft Defender: Complete Guide www.itprofessor.clou...
#MicrosoftDefender #DefenderforCloud #Security #MicrosoftSecurity #Cybersecurity #DefenderXDR #MicrosoftThreatIntelligence

A new era of agents, a new era of posture www.microsoft.com/en...
#MicrosoftDefender #DefenderforCloud #Security #MicrosoftSecurity #Cybersecurity #DefenderXDR #MicrosoftThreatIntelligence

Determine Defender for Endpoint offboarding state for Linux devices techcommunity.micros...
#MicrosoftDefender #DefenderforCloud #Security #MicrosoftSecurity #Cybersecurity #DefenderXDR #MicrosoftThreatIntelligence

Change to auto-remediation in Defender for Office socautomators.substa...
#MicrosoftDefender #DefenderforCloud #Security #MicrosoftSecurity #Cybersecurity #DefenderXDR #MicrosoftThreatIntelligence

Secure collaboration in Microsoft Teams with efficient and automated Threat Protection and response techcommunity.micros...
#MicrosoftDefender #DefenderforCloud #Security #MicrosoftSecurity #Cybersecurity #DefenderXDR #MicrosoftThreatIntelligence

Determine Defender for Endpoint offboarding state of Windows machines using PowerShell techcommunity.micros...
#MicrosoftDefender #DefenderforCloud #Security #MicrosoftSecurity #Cybersecurity #DefenderXDR #MicrosoftThreatIntelligence

Introducing AI-powered incident prioritization in Microsoft Defender techcommunity.micros...
#MicrosoftDefender #DefenderforCloud #Security #MicrosoftSecurity #Cybersecurity #DefenderXDR #MicrosoftThreatIntelligence

Introducing the Microsoft Defender Experts Suite: Elevate your security with expert-led services www.microsoft.com/en...
#MicrosoftDefender #DefenderforCloud #Security #MicrosoftSecurity #Cybersecurity #DefenderXDR #MicrosoftThreatIntelligence

Announcing public preview: Uncovering hidden threats with the Dynamic Threat Detection Agent techcommunity.micros...
#MicrosoftDefender #DefenderforCloud #Security #MicrosoftSecurity #Cybersecurity #DefenderXDR #MicrosoftThreatIntelligence
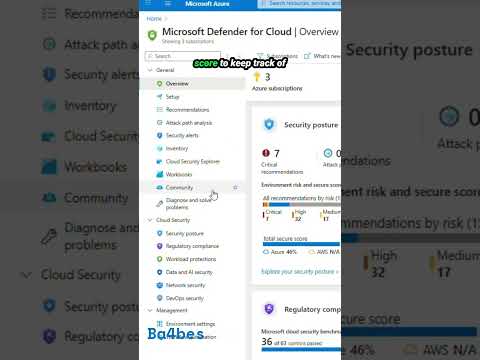
Day 23 brings Microsoft Defender for Cloud, and in One Minute of Azure we cover how it spots risks across your resources and helps tighten your security posture.
#Azure #DefenderForCloud #CloudSecurity #SecurityPosture #OneMinuteOfAzure
youtube.com/shorts/YBLbu...

𝐍𝐞𝐰 𝐛𝐚𝐝𝐠𝐞 𝐮𝐧𝐥𝐨𝐜𝐤𝐞𝐝: 𝐒𝐞𝐜𝐮𝐫𝐢𝐭𝐲 𝐂𝐨𝐦𝐦𝐮𝐧𝐢𝐭𝐲 𝐈𝐧𝐟𝐥𝐮𝐞𝐧𝐜𝐞𝐫 2025
www.credly.com/badges/961bb...
#MVPBuzz #OZPerts #followoz #CloudSecurity #Azure #DefenderForCloud #MicrosoftSentinel #CNAPP #DevSecOps #Terraform #IaC #Community #Panama #MicrosoftSecurity

Demystifying AI Security Posture Management techcommunity.micros...
#MicrosoftDefender #DefenderforCloud #Security #MicrosoftSecurity #Cybersecurity #DefenderXDR #MicrosoftThreatIntelligence

Microsoft Defender: Smart Containment Stops Exposed Privileged AD Domain Accounts techcommunity.micros...
#MicrosoftDefender #DefenderforCloud #Security #MicrosoftSecurity #Cybersecurity #DefenderXDR #MicrosoftThreatIntelligence

The Microsoft Defender for AI Alerts techcommunity.micros...
#MicrosoftDefender #DefenderforCloud #Security #MicrosoftSecurity #Cybersecurity #DefenderXDR #MicrosoftThreatIntelligence

Microsoft Defender Experts - S.T.A.R. Series techcommunity.micros...
#MicrosoftDefender #DefenderforCloud #Security #MicrosoftSecurity #Cybersecurity #DefenderXDR #MicrosoftThreatIntelligence

Microsoft Defender for Cloud Customer Newsletter techcommunity.micros...
#MicrosoftDefender #DefenderforCloud #Security #MicrosoftSecurity #Cybersecurity #DefenderXDR #MicrosoftThreatIntelligence

Beyond Visibility: Hybrid Identity Protection with Microsoft Entra & Defender for Identity techcommunity.micros...
#MicrosoftDefender #DefenderforCloud #Security #MicrosoftSecurity #Cybersecurity #DefenderXDR #MicrosoftThreatIntelligence

Key findings from product telemetry: top storage security alerts across industries techcommunity.micros...
#MicrosoftDefender #DefenderforCloud #Security #MicrosoftSecurity #Cybersecurity #DefenderXDR #MicrosoftThreatIntelligence

Defender for AI services: Threat Protection and AI red team workshop techcommunity.micros...
#MicrosoftDefender #DefenderforCloud #Security #MicrosoftSecurity #Cybersecurity #DefenderXDR #MicrosoftThreatIntelligence

Strengthening calendar security through enhanced remediation techcommunity.micros...
#MicrosoftDefender #DefenderforCloud #Security #MicrosoftSecurity #Cybersecurity #DefenderXDR #MicrosoftThreatIntelligence

Using the Microsoft Defender for Endpoint Files API to Validate Malware Hashes techcommunity.micros...
#MicrosoftDefender #DefenderforCloud #Security #MicrosoftSecurity #Cybersecurity #DefenderXDR #MicrosoftThreatIntelligence